Ribbon Cuttings

Seniors Helping Seniors Celebrates First Anniversary in Oklahoma City
EDMOND, OK – Seniors Helping Seniors recently held a ribbon cutting with the Edmond Area Chamber of Commerce to celebrate their first anniversary at 100 NE 5th Street. At Seniors Helping Seniors® Central Oklahoma, the core values drive every aspect of service provision. The organization believes in the power of seniors helping each other […]
Read more »
Edmond Public School Foundation Celebrates the Upcoming Inaugural EDIEE Awards with Ribbon Cutting
Edmond Public School Foundation held a ribbon cutting with the Edmond Chamber of Commerce at 4800 N Kelly Ave. The Edmond Public Schools Foundation is thrilled to announce the inaugural EDIEE Awards ceremony, scheduled for Tuesday, April 16, at Aspen Ranch in Edmond. Established in 1984, the Edmond Public Schools Foundation will celebrate its 40th […]
Read more »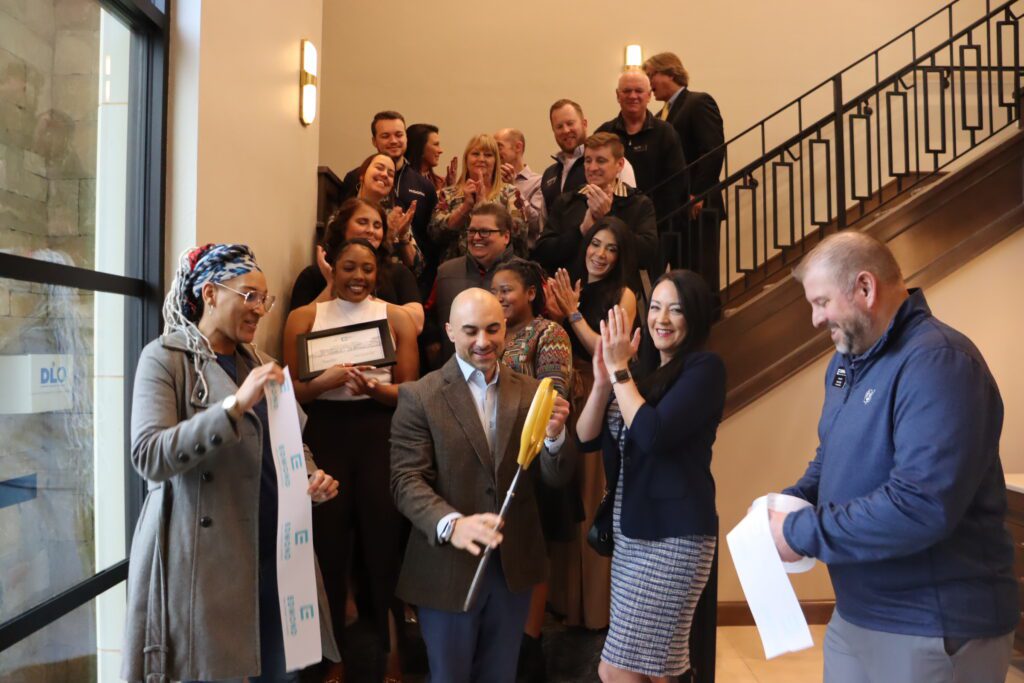
Evoke 5 Medical Center Celebrates Open House with Ribbon Cutting
Evoke 5 Medical Center held a ribbon cutting with the Edmond Chamber of Commerce at 401 S. Coltrane Rd Ste 280. Evoke 5 Medical Center offers Primary Care + Functional Medicine. The care at their family medicine clinic is based on the 5 Pillars of Health & Wellness©, an approach developed and refined by Evoke5 […]
Read more »
Oklahoma ER & Hospital Celebrates 5th Anniversary with Ribbon Cutting
Oklahoma ER & Hospital held a ribbon cutting with the Edmond Chamber of Commerce at 15103 N Pennsylvania Avenue. Oklahoma ER & Hospital is a part of Nutex Health (NASDAQ: NUTX), being the 1st specialty hospital to bring the communities in Oklahoma accessible, concierge-level emergency care they can trust. Their team utilizes the same cutting-edge […]
Read more »
Edmond Music Celebrates 50th Anniversary with Ribbon Cutting
Edmond Music held a ribbon cutting with the Edmond Chamber of Commerce at 3400 S Broadway. Edmond Music is a family owned local music store serving the greater Oklahoma City area for more than forty years. Their knowledgeable staff works to bring you the best in musical instruments and service at the most competitive prices. […]
Read more »
Stretch U Offering Strategic Stretching Services to Clients in Edmond
Stretch U held a ribbon cutting with the Edmond Chamber of Commerce at 331366 east Hwy 66. Stretch U started in Oklahoma City when Physical Therapist John Carey began bringing his massage table to family gatherings and stretching family members. Stretch U provides full-body one-on-one assisted stretching in 20, 40, and 60-minute appointments. We utilize a […]
Read more »
Parcel Goods + Gifts Celebrate Grand Opening at Edmond Location
Parcel Goods + Gifts held a ribbon cutting with the Edmond Chamber of Commerce at 140 E 5th Street, Ste 100. Parcel Goods + Gifts is a local, family owned business that strives to curate memorable gifts for the community. Their team believes that gifting well is committing to loving well. Their collections are curated […]
Read more »
Vignolas Italian Kitchen Celebrate Grand Opening at Edmond Location
Vignolas Italian Kitchen held a ribbon cutting with the Edmond Chamber of Commerce at 23 W 1st St, Suite 130. Vignolas Italian Kitchen is a family owned-and-operated restaurant located in the Edmond Railyard that will offer authentic Italian comfort food. Owners Ashley and Giovanni Vignola opened their doors on December 4, 2023 to the community […]
Read more »
Pampered Pets Celebrate Anniversary at Edmond Location
Pampered Pets Veterinary Clinic and Spa held a ribbon cutting with the Edmond Chamber of Commerce at 2020 N. Kelly Avenue. The team at Pampered Pets Veterinary Clinic and Spa are Oklahoma pet lovers just like you! They designed their services to meet the needs of all lovable pets. Dr. J. Brian Ledger, veterinarian and […]
Read more »
Linden Salon Celebrates Grand Opening at Edmond Location
Linden Salon held a ribbon cutting with the Edmond Chamber of Commerce at 17 W 1st Street suite 100. Linden Salon specializes in color and extension services. Their hairstylists take pride in offering their clients an elite hair experience. They offer a beautifully curated space for clients to enjoy while having thoughtful conversations about their […]
Read more »
Eros Health Celebrates Grand Opening at new OKC Location
Eros Health is excited to provide health and wellness care to the Edmond community and surrounding areas from their new location at 13921 N Meridian, ste 103, OKC. EROS Health is a health and wellness clinic for both men and women, that is Urologically based. For men, they offer a full range of ED treatments catered […]
Read more »
McDonalds Welcoming Back Customers to N. Kelly Ave Location
McDonalds held a ribbon cutting with the Edmond Chamber of Commerce at 1235 N Kelly Ave. M2U Enterprises, Inc. is an independent franchise of McDonald’s which owns and operates the N Kelly Ave location along with 6 other locations in the state. Their team is comprised of hard-working people who all contribute to providing the […]
Read more »
Chico’s Mexican Restaurant Celebrates Grand Opening at Edmond Location
Chico’s Mexican Restaurant held a ribbon cutting with the Edmond Chamber of Commerce at 1389 E. 15th Street. Chico’s Mexican Restaurant is a family owned business, with the original restaurant kickstarting in Stillwater 2 years ago. Their family recipes originate from Jalisco, Mexico where they also manage other restaurants. They have now opened another location […]
Read more »
Balanced Kitchen Co. Providing Healthier Food Alternatives From Their New Edmond Location
Balanced Kitchen Co. held a ribbon cutting with the Edmond Chamber of Commerce at 740 West Danforth Road. Balanced Kitchen is a meal prep restaurant with a mission to make eating well easy and enjoyable. Born in the midst of the pandemic in 2020, Balanced Kitchen Co. focuses on providing the everyday person delicious, nutritious […]
Read more »
Andy B’s Celebrates Grand Opening after ‘rolling in’ new Oklahoma City Location
Andy B’sheld a ribbon cutting with the Edmond Chamber of Commerce at 11917 N Pennsylvania Ave in Oklahoma City. The business features luxury VIB bowling powered by Spark©, a full-service restaurant and bar, a modern arcade, indoor axe-throwing with automatic scoring, duckpin bowling, and more, Andy B’s will have something for everyone. Heritage Lanes was […]
Read more »
Homeland Celebrates Grand Opening at new Edmond Location
Homeland held a ribbon cutting with the Edmond Chamber of Commerce at 16525 Rose Creek Blvd. located inside the Rose Creek Plaza. Homeland is set to become the go-to destination for locals seeking fresh, high-quality meat and produce, exceptional variety, and unique services. Customers can expect an array of organic and conventional products to meet […]
Read more »
Edmond Wine Shop Celebrates 50 Years of their Full-Service Wine, Spirit and Beer Business
Edmond Wine Shop held a ribbon-cutting with the Edmond Chamber of Commerce at 1520 South Boulevard in Edmond. Edmond Wine Shop is a full-service wine, spirit & beer retailer in Edmond. The store was founded in November, 1973, by Vance Gregory who believed that Edmond consumers deserved to have a local fine wine resource modeled […]
Read more »
The Richards Group Celebrate Grand Opening at new Edmond Location
The Richards Group held a ribbon cutting with the Edmond Chamber of Commerce at 3412 NW 178th St., Ste A. The Richards Group is an independent insurance agency under Legacy Insurance. They are a family-owned business, striving for excellence with upmost customer service in mind. By building long-standing customer relationships, they desire to find their […]
Read more »
LoFi Dental Celebrate Ribbon Cutting at Edmond Location
LoFi Dental held a ribbon cutting with the Edmond Chamber of Commerce at 5349 E Covell Rd. LoFi Dental is a dentist establishment with a philosophy focusing on meeting people where they are, and taking them where they want to be. Through modern care and cozy vibes, LoFi Dental redefines the dental experience and transforms […]
Read more »
Jamba Juice and Auntie Anne’s Celebrate Grand Opening at new Edmond Location
Jamba Juice and Auntie Anne’s held a ribbon cutting with the Edmond Chamber of Commerce at W 15th St. Jamba Juice and Auntie Anne’s opened a new co-brand location offering both delicious smoothies, pretzels and more! For nearly 30 years, Jamba has brought the right, delicious ingredients to create whirl’d famous flavor served by friendly […]
Read more »
Crest Foods Celebrate Grand Opening at new Edmond Location
Crest Foods held a ribbon cutting with the Edmond Chamber of Commerce at 2933 N Sooner Rd. Crest has been providing customers with discount prices, clean stores, and friendly service ever since the beginning! In 1929, Crest founder Nicola Harroz, Sr. opened the family’s first grocery store, Fairview Grocery, at Southwest 29th and Agnew. This […]
Read more »
Valir Physical Therapy Now Servicing Patients at new Edmond Location
Valir Physical Therapy held a ribbon cutting with the Edmond Chamber of Commerce at 17860 N MacArthur Blvd Ste E. Physical therapists at Valir Physical Therapy are highly trained specialists that can assist you with a variety of pain issues, injuries, and discomfort. Valir now operates 21 outpatient physical therapy locations across the state. To learn more […]
Read more »
Dave’s Hot Chicken Celebrates Grand Opening of Edmond Location
Dave’s Hot Chicken recently held a ribbon cutting with the Edmond Area Chamber of Commerce to celebrate their grand opening at 2404 E 2nd St. Dave’s Hot Chicken is a restaurant based out of LA and recently franchised to Oklahoma! Their first location within Oklahoma was in Bricktown and now they’re expanding into the […]
Read more »
Believe and Succeed Celebrates Grand Opening in Edmond
Believe and Succeed recently held a ribbon cutting with the Edmond Area Chamber of Commerce to celebrate their grand opening at 6933 E Waterloo Rd, Suite 2. Believe & Succeed, LLC is thrilled to announce the opening of its office, offering a transformative approach to personal growth and well-being. Owned and operated by Elizabeth Schultz, […]
Read more »